Ultimate Guide to Website Security Analysis
Staying one step ahead of the latest cybercrime strategies is no easy feat. Attacks can have major consequences, with the average cost of a data breach in 2023 being $4.45 million. Conducting regular security audits empowers WordPress site owners to stay one step ahead of risks, protecting sensitive user data and maintaining consumer trust.

Staying one step ahead of the latest cybercrime strategies is no easy feat. Attacks can have major consequences, with the average cost of a data breach in 2023 being $4.45 million.
Conducting regular security audits empowers WordPress site owners to stay one step ahead of risks, protecting sensitive user data and maintaining consumer trust. Audits also help to ensure compliance with regulatory standards, ensuring your brand works within legal guidelines.
Our ultimate guide to website security analysis will delve into audit types, common methods of cyber attack, and proactive measures that site admins can implement to reduce threats. We’ll also explore the advantages of automated security audits, such as those offered by Solid Security, which provide premium protection while reducing the need for manual input.
Types of security audit
Different auditing methods come with different benefits and use cases — let’s take a look at the three main types available:
Automated security audits
Automated security audits use specialized tools to scan websites for vulnerabilities and security weaknesses. The primary benefits of automation are speed, efficiency, and the ability to cover a range of issues without human intervention. Solid Security’s automated scanning capabilities seamlessly integrate with Patchstack in our Pro version, providing real-time vulnerability detection and automated patching.
Manual security audits
This is when real people analyze and interpret the results from automated tools, providing a more in-depth assessment of your website’s security. The main advantage of manual audits is their ability to identify false positives and provide detailed insights that automated tools might miss. Solid Security’s dashboard offers both single and scheduled reports and insights, combining manual work with automatic analysis.
Professional security audits
For this type of audit, you call a cybersecurity expert who uses advanced techniques and tools to identify and resolve vulnerabilities. While this approach provides the highest level of security assurance with expert analysis and tailored solutions, it also involves the expense of hiring cybersecurity consultants. However, Solid Security’s user-friendly software is easy for non-techies to use, saving you the cost of paying a professional.
In summary, regular security audits are essential to guard against potential threats, and automated versions offer the most convenient solutions for busy site owners and dev teams. Remember to also conduct an audit prior to the launch of a new website. If you’ve a project on the brink of going live, refer to our in-depth website launch checklist to find out more.
Identifying common website vulnerabilities
Here we’ll detail the most common website vulnerabilities that every online business should be aware of.
Structured Query Language (SQL) Injection

In SQL injection, malicious SQL code is used to manipulate backend databases. Attackers exploit vulnerabilities in web applications to inject malicious queries, potentially leading to unauthorized access, data deletion, and database manipulation. Common causes of SQL injection include inadequate input sanitization and insecure coding practices.
One famous SQL attack involved Sony Pictures in 2011. Around 77 million Playstation accounts were hacked and their personal details exposed. The incident cost Sony $170 million, and is a welcome reminder that no company is ever too big for a data breach.
Cross-Site Scripting (XSS)
XSS involves injecting malicious scripts into web applications to target users. Attackers exploit vulnerabilities to execute scripts in users’ browsers, potentially stealing data, hijacking sessions, and defacing websites. Insufficient input validation and output encoding are common causes of XSS vulnerabilities.
In 2018, British Airways (BA) fell victim to an XSS attack that compromised customer payment information. A hacking group exploited an XSS vulnerability in a JavaScript library that was used on the BA website. The script was modified to send customer data to a different server, which even had its own Secure Sockets Layer (SSL) certificate! 380,000 credit card transactions were made before the scam was discovered.
Remote File Inclusion (RFI)
RFI occurs when attackers remotely inject files into a web application server. This vulnerability can lead to server compromise, data theft, and malware distribution. Improper validation of file paths and URLs is a common cause of RFI vulnerabilities.
The Panama Papers incident in 2016 involved a likely RFI attack that led to the exposure of the financial dealings of public figures. Given that some of these were less than legitimate, the breach led to resignations, arrests, and global scandal.
Cross-Site Request Forgery (CSRF)
CSRF is an attack that tricks users into performing unwanted actions on a web app they are authenticated on. Attackers exploit the trust between the user’s browser and the web application, potentially leading to unauthorized fund transfers, password changes, and data manipulation. CSRF attacks often occur due to a lack of anti-CSRF tokens and improper session management.
In 2009, a CSRF vulnerability in uTorrent’s web console allowed attackers to deploy malware on users’ devices and change admin passwords via simple GET requests. Exploiting uTorrent’s improper implementation of state-changing operations, attackers used malicious HTML elements on forums and in emails to target users.
To prevent CSRF attacks, we recommend implementing unique CSRF tokens for sensitive user requests and properly validating these tokens when processing the requests.
Vulnerabilities from third-party components
Third-party components, such as open-source software applications like plugins and themes, can introduce vulnerabilities to websites if not regularly updated or scanned. These vulnerabilities can lead to data breaches, as seen in the 2017 Equifax incident, where a failure to patch a known vulnerability in Apache Struts led to the exposure of sensitive information for 147 million people.
Automating security audits with Solid Security
Solid Security’s automated scanning capabilities play a crucial role in identifying and resolving website vulnerabilities. By proactively detecting potential threats, Solid Security allows site owners to take action and maintain a secure online presence. Let’s see how!
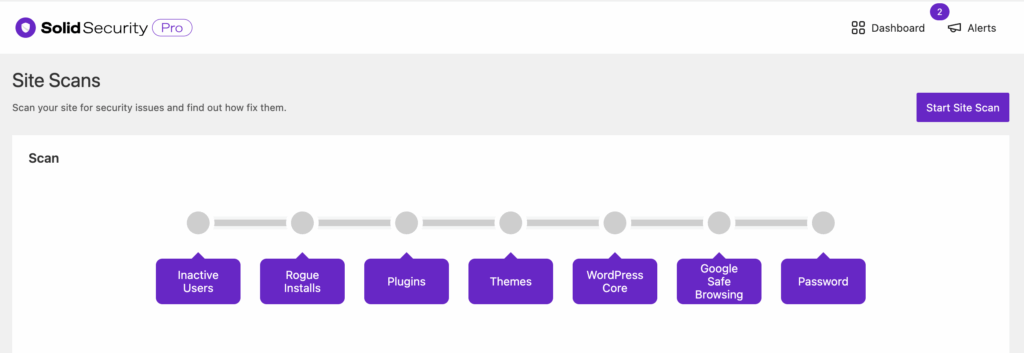
Utilizing Solid Security’s scanning capabilities
- Types of scans performed: Solid Security performs comprehensive scans that cover inactive users, rogue installations, plugins, themes, and WordPress core files. By thoroughly examining each of these components, Solid Security ensures that no stone is left unturned in the hunt for vulnerabilities.
- Detailed information on detected vulnerabilities: The plugin offers insights into vulnerability type, scan information, severity level, and recommended actions. With a user-friendly interface, our platform makes it easy for website owners to interpret the scan results, so swift action can be taken.
- Firewall integration: A built-in firewall feature actively blocks malicious traffic, providing real-time logs of thwarted threats. Users can also create custom rules to automate site protection, improving the overall security of their website.

Solid Security’s automated scans can save you valuable time and reduce the need for manual security checks. Our plugin’s continuous monitoring provides peace of mind, so you can focus on growing your brand, safe in the knowledge that your site is protected.
Integrating with Patchstack for enhanced protection

Patchstack integration offers an additional layer of protection for WordPress websites. In 2024, Patchstack introduced a new firewall engine, engineered to deliver the most efficient application layer protection possible. Its extensive library of 7,000 individual vPatch rules provides the largest vulnerability coverage on the market, benefitting users on our Solid Security Pro plans.
vPatches are prepared, tested, then auto-deployed to sites immediately when a vulnerability is detected. A rapid response system ensures that websites are protected against newly discovered threats with minimal delays.
In addition to its vPatch system, Patchstack includes a generic OWASP protection module. This incorporates firewall rules designed to defend against OWASP’s top 10 vulnerability types, including XSS, SQL injection, and SSRF.
Solid Security’s Patchstack partnership provides protection against high- and medium-severity vulnerabilities, ensuring continuous and automated protection with no need for manual intervention.
Proactive measures for continuous security
While regular, automated audits make a massive contribution to overall website security, site owners can further harden their defenses by adopting the following proactive measures. These reduce opportunities for hackers to attempt entry to your site:
- Two-Factor Authentication (2FA): 2FA adds an extra layer of security by requiring a second form of verification before granting access. This can include SMS codes, authentication apps, or biometric verification. Solid Security supports 2FA implementation, securing user logins and making attempts at unauthorized access much harder.

- Additional login security: Additional login security measures like limiting login attempts, enforcing strong passwords, and implementing passkeys are also worth implementing. Solid Security uses these features to protect websites against DDoS and brute force attacks.
- Zero-trust architecture: Zero-trust architecture, based on the principle of ‘never trust, always verify’, enforces strict access controls and the continuous monitoring of all users and devices. This approach assumes that threats can come from both inside and outside the network, covering all potential bases.
- DevSecOps practices: Integrating DevSecOps practices into the software development lifecycle is a great security measure. This approach incorporates security at every stage, promoting secure coding practices, regular code reviews, and the use of automated testing tools.
- SSL implementation: Proper implementation of an SSL certificate encrypts interactions between customers and your site, and certificates are available free of charge. Our centralized management platform Solid Central can scan your existing SSL to identify mixed content or other issues, ensuring everything is set up correctly.
- Ongoing training and awareness: Regular training and awareness programs for employees and users can help reduce social engineering attacks and other human-related vulnerabilities. Our own Solid Academy includes tutorials, guides, and courses relating to WordPress, with lots of security news and information.
- Continuous monitoring and real-time threat detection: Continuous monitoring allows threats to be identified and handled in real-time, rather than giving them time to mature, spread, and cause greater damage. Solid Security’s real-time dashboard and automated alerts enable quick responses to threats whenever they occur.
Recovering from security incidents
While proactive security measures combined with regular audits reduce the risks associated with cybercrime, no system is entirely impenetrable. If a breach occurs, don’t panic — it’ll likely happen at some time in your site’s existence, so having an effective response in place is a must-have. Take the following steps to ensure a swift recovery:
- Act fast and contain the issue: Quickly isolate affected systems and networks to prevent the breach from spreading. Solid Security’s real-time monitoring and alerts can help limit any potential damage.
- Assess the issue: Determine the scope of the breach, the type of data compromised, and the potential impact on users. Involve law enforcement and relevant authorities if necessary to ensure compliance with legal requirements and aid in the investigation.
- Remove: Once the assessment is complete, eliminate the root cause of the breach. This may involve patching vulnerabilities, updating software, or removing malware. Solid Security Pro’s integration with Patchstack can identify and patch vulnerabilities, ensuring all systems are clean before restoration.
- Restore: Restore affected systems and data from clean backups. Our cloud-first backup solution, Solid Backups — NextGen offers one-click restoration, providing a reliable solution for data recovery. Those with multiple sites will also benefit from adopting Solid Central — a WordPress site management tool — and our Solid Suite combines Solid Security, Solid Backups, and Solid Central for a discounted price.
- Notify: Promptly notify affected users, providing guidance on how they can protect themselves from potential identity theft or other consequences. Remember that transparency and clear communication will help to maintain user trust during any data breaches.
- Post-incident analysis: Conduct a thorough post-incident analysis to understand how the breach occurred and identify areas for improvement. Implement lessons learned and update security policies accordingly.
- Adopt a preventative measure: To strengthen your defenses against future threats, consider using a premium solution like Solid Security. Features like automatic updates and real-time monitoring provide robust protection against a wide range of cyber threats, while vulnerability scans can be filtered to a whole site, or specific areas like the WordPress core.

Next steps: Secure your site with Solid Security
“Security audits are central to effective website management. They proactively identify vulnerabilities, ensure compliance, protect sensitive data, and maintain customer trust. For businesses to thrive online, regular security audits are not an option, but an absolute necessity.”
Jennifer Schramm, Director of Product Marketing, SolidWP
As we’ve seen, neglecting security can have major consequences for your business, resulting in data breaches, loss of customer trust, and financial losses. Adopting stringent security measures protects your site and provides peace of mind when moving forward.
Solid Security is explicitly designed to guard your WordPress site against evolving threats. With features like two-factor authentication, vulnerability scanning, and firewall protection, you’ll gain an impressive defense against potential attacks. Detailed security logs offer insights into your site’s security status, while our integration with Patchstack protects against newly discovered vulnerabilities — taking action when you can’t.
Don’t wait for a security breach before shoring up your own website — take proactive steps to secure your digital assets by trying Solid Security today.
Sign up now — Get SolidWP updates and valuable content straight to your inbox
Sign up
Get started with confidence — risk free, guaranteed
